AI agents and copilots are quickly becoming essential to compete. Organizations are racing to deploy them, and in doing so, are dramatically expanding their identity surface.
While identity sprawl is the visible symptom, the bigger issue is uncontrolled execution at runtime. Enterprises still lack reliable governance over how these agents operate once they’re live in production, especially as they become more autonomous. They lack control over what data agents can access, what derivative data they create, what actions they trigger downstream, and whether that behavior remains appropriate over time.
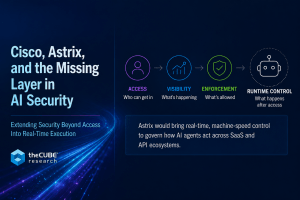
Cisco’s planned acquisition of Astrix Security is about establishing runtime control for AI agents and other non-human identities, and in doing so enabling AI to be secured in production.
From Identity Management to Runtime Enforcement
Astrix’s framing underscores how far ahead deployment is relative to control. Non-human identities already outnumber humans by orders of magnitude, they’re frequently overprivileged, and, very often, they operate without clear ownership or auditability.
Beyond identity sprawl, enterprises are contending with a layer of autonomous activity that is largely ungoverned, and is already starting to influence critical business operations.
Most existing security controls were built for a different operating model. Identity and Access Management (IAM) governs user access at login. Privileged Access Management (PAM) manages privileged sessions. SaaS Security Posture Management (SSPM) surfaces SaaS misconfigurations.
None of these map cleanly to environments where agents are making decisions, APIs are interacting continuously, and access to data is persistent and machine-driven.
Astrix’s approach addresses not only visibility and security posture, but also runtime control:
- Discovery: Customers can build a live inventory of agents, integrations, and non-human identities, including shadow and third-party
- Security Posture: The offering identifies overprivileged access, anomalous behavior, and policy violations.
- Deployment: Astrix enforces least privileged access, short-lived credentials, and scoped access by design.
The key value is the ability to establish guardrails around how AI systems operate once they’re in production, observing, constraining, and validating how autonomous actions are executed across environments.
Why This Matters
AI agents are active participants in enterprise workflows, often operating with broad delegated access. They go beyond retrieving data, taking actions and chaining together multiple systems through APIs. In many cases, that access is persistent rather than session-based.
For example, an AI agent connected to a SaaS platform via OAuth may be granted broad access to customer data, generate derivative datasets, and trigger downstream workflows across multiple systems. That access often persists well beyond a single session, with limited visibility into how it is being used or whether it remains appropriate.
Without runtime controls, overprivileged and shadow agents become high-impact attack paths because there is limited ability to trace or constrain behavior in real time. In other words, AI agents are not yet consistently operationalized safely at scale.
What Astrix Would Add to Cisco
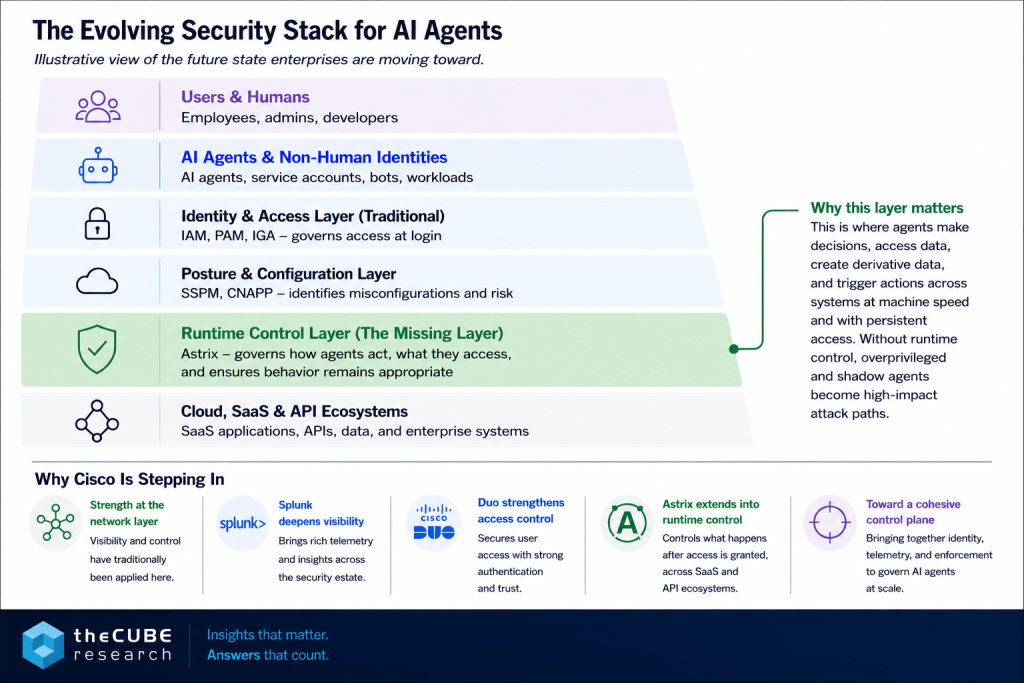
Cisco has been building a security architecture that spans access, telemetry, and enforcement, grounded in its strength at the network layer, where visibility and control have traditionally been applied.
The addition of Splunk deepened its visibility into security operations. Duo Security strengthens control over user access. Astrix would extend this architecture into a critical gap: controlling what happens after access is granted, at machine speed, across SaaS and API ecosystems.
This starts to align with a broader shift in how control is applied. Not just at the point of access, but across the flow of interactions between systems. This layer becomes essential as AI agents begin to operate at scale.
Execution will matter. Cisco has assembled many of the right pieces, but integrating visibility, detection, and enforcement into a cohesive control plane will be a complex task that requires stitching together multiple products into a unified operational experience.
Where the Market Is Headed
This isn’t a cleanly defined category yet, but it highlights a gap the market hasn’t fully addressed, between managing identity and controlling how that access is used in practice.
Identity needs to expand beyond authentication into continuous validation of behavior. SaaS security needs to move past posture toward active enforcement of interactions. And AI security needs to evolve beyond how models behave in isolation, becoming a question of how agents are governed in real production environments. To that point, the control plane itself needs to shift closer to execution.
The Bottom Line
Cisco’s interest in Astrix reflects that enterprises are moving toward a future where they will rely on hundreds or thousands of AI agents to support core business functions, but they currently have very limited ability to control what those agents actually do in production.
Astrix presents an opportunity for Cisco to advance one of the most important control points in the future security stack: securing AI in runtime.