Enterprise security teams have spent years expanding prevention and detection capabilities across identity, endpoints, networks, applications, and cloud environments. Identity is evolving from a provisioning and access function into a central security control plane shaped by zero trust initiatives, PAM, and increasingly identity-driven attacks. Security operations is expanding beyond traditional SIEM workflows as endpoint, cloud, network, and identity telemetry converged into XDR and broader detection ecosystems.
At the same time, cloud architectures add a new layer of operational complexity. Security teams are adapting to dynamic workloads, SaaS sprawl, APIs, containers, and continuously changing configurations, driving growth in posture management, workload protection, and cloud-native security platforms.
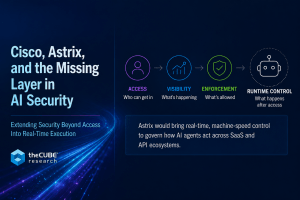
AI is accelerating many of these pressures. Enterprises are managing growing volumes of machine identities, faster attack cycles, increased automation, and expanding data exposure through AI services and copilots. Security teams are simultaneously being asked to move faster while processing even larger volumes of telemetry, alerts, and operational context.
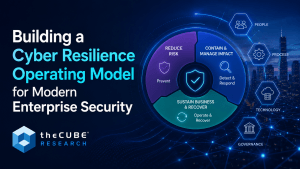
These pressures are driving organizations to expand security operating models beyond prevention and incident response alone. Security teams are now expected to manage more than threat detection and containment. They are increasingly responsible for helping organizations sustain operations during an attack, coordinate recovery efforts, support executive decision-making, and restore business services under pressure.
What is emerging is the need for an operational model that connects traditional security functions of prevention, detection and incident response, with the ability to operate through and recover from attacks.
The New Attack Surface Stress-Tests Preventive Security Models
Preventive security capabilities such as least privilege access and misconfiguration and vulnerability management remain foundational. These capabilities reduce exposure and limit exploitability, and every improvement in prevention reduces downstream operational disruption. at the same time, identity-driven attacks, API exposure, cloud misconfigurations, and highly distributed environments continue increasing enterprise risk. The scale and complexity of modern attack surfaces are making it harder for organizations to reduce operational risk through prevention alone.
Security Operations No Longer End at Containment
Ransomware, cloud compromise, and identity-driven attacks have pushed security operations beyond monitoring and alert management. Threat hunting, containment, investigation, and remediation workflows have become critical as identifying and containing active threats faster become more important.
The SOC is the operational hub for cybersecurity detection, investigation, and incident response. But the responsibilities surrounding a major cyber incident do not stop with containment.
Security teams may isolate systems or remove attackers from the environment, but business disruption continues long after the immediate threat is contained. Critical systems still need to come back online. Data integrity still needs validation. Employees need guidance. Executives need coordinated decision-making under pressure. Customers, partners, and regulators may also require communication and ongoing updates.
This is where the boundaries between security operations, IT operations, business continuity, and crisis management start to blur.
The organizations navigating these incidents most effectively are increasingly the ones that can coordinate across those functions instead of managing them as disconnected operational domains.
Operate and Recover Rises as a Strategic Priority
The ability to operate through disruption and recover quickly after a cyber event is becoming a central part of the enterprise security operating model.
Historically, functions such as operational fallback procedures, recovery orchestration, immutable recovery environments, crisis management, and post-incident adaptation. Historically operated adjacent to cybersecurity rather than as part of a unified operating model.
Functions such as operational fallback procedures, recovery orchestration, immutable recovery environments, crisis management, and post-incident adaptation have traditionally operated adjacent to cybersecurity rather than as part of a coordinated operational model.
That separation is becoming harder to sustain.
Attackers do not operate according to organizational charts. An identity compromise becomes a cloud incident. A cloud incident becomes an operational outage. An outage quickly becomes a business continuity issue with executive-level implications.
Organizations that navigate these transitions effectively tend to have stronger coordination across security operations, IT operations, business continuity, risk management, and executive leadership.
Organizations that struggle often discover that their teams, processes, and technologies were never designed to coordinate effectively during disruption.
Why the Cyber Resilience Operating Model Matters
This shift is changing how enterprises evaluate security strategy, operational readiness, and technology investment.
Security leaders are paying closer attention to how prevention, detection, recovery, and operational continuity connect together. Data recovery is increasingly part of security strategy discussions. Identity is becoming a central control plane across all three operational layers. Security operations platforms are under pressure to provide business context and prioritization instead of simply surfacing alerts.
The vendor landscape is shifting alongside it.
Security vendors are expanding into resilience and recovery. Backup and data protection vendors are moving deeper into cyber detection and response. Platform narratives increasingly focus on operational coordination across the full incident lifecycle.
Some of this reflects legitimate market evolution. Some reflects the industry’s tendency to repackage existing capabilities around the latest narrative cycle.
Either way, enterprise expectations are changing.
Cybersecurity and Cyber Resilience Are Becoming More Operationally Connected
Cybersecurity increasingly functions as part of a broader operational strategy focused on reducing risk, managing disruption, and sustaining business operations during a cyber event.
That transition is still underway inside many enterprises. But organizations are increasingly recognizing that resilience is not separate from cybersecurity operations. It is becoming part of how enterprises prepare for, respond to, recover from, and adapt to disruption.
This shift is driving closer coordination across prevention, detection and response, recovery, business continuity, IT operations, and executive decision-making.
The organizations adapting most effectively are treating these functions less as isolated operational domains and more as interconnected parts of a broader resilience operating model.